Welcome to Come2U Computer Services
I hope you enjoy my Posts :)
Welcome to Come2U Computer Services
I hope you enjoy my Posts :)
We now have a female tech who can assist NDIS type customers with computer help & tuition.Bookings required.
I still like my Waze.
https://cyberguy.com/software/google-maps-vs-waze-vs-apple-maps-best

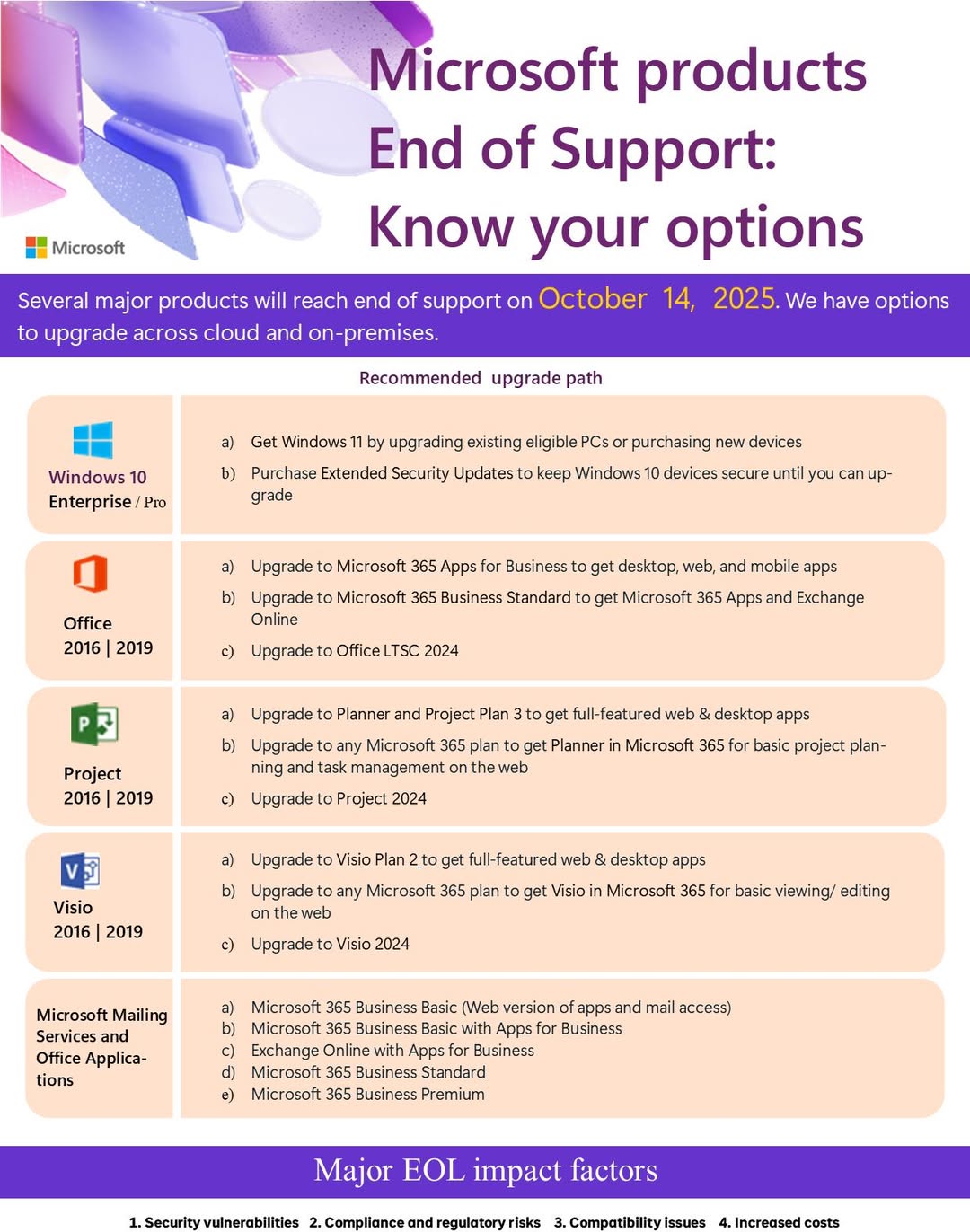
🔧 Upgrade to stay ahead of:
✅ Security vulnerabilities
✅ Compliance risks
✅ Compatibility issues
✅ Rising IT costs
💼 Choose your upgrade path:
🔹 Windows 11
🔹 Microsoft 365 Business Plans
🔹 Office LTSC 2024
🔹 Project & Visio 2024
🔹 Planner, Exchange Online, and more!
📢 Future-proof your infrastructure today! Talk to us today.

https://www.xda-developers.com/how-to-spot-counterfeit-hdd
Of course if you buy from us we do all the checks and you only get certified genuine parts.

Hi Everyone,
Interesting article from one of my nerd feeds this morning.
Seems some older TP Link Routers are hijacking Office 365 credentials…which is not good…see story link below.
https://www.tomsguide.com/…/tp-link-router-flaws-lets…
My advice
Check you modem/router is not using the default password to get into it’s web interface confirguration page. If it is change it as soon as you can.
Check if your modem or router has a firmware update available…if so get the update done asap (your internet providers support team will probably do this)
If your modem is already end of life (normally the modem’s manfacturers or your internet service providers support page will tell you this) you should replace your modem. You should purchase a new one off your internet provider (less hassel as they will often send you a new one preconfigured)
As a general rule if you modem/router is anymore than say 4-5 years old you should replace it. Benefits of replacing it is that you will probably get a better and more stable internet connection speed and your wifi will be faster (because of the new WiFi 7 speeds in modems now) and you will be more secure.
As always – we can sort all this for you. Just call us.
I don’t trust any VPN Provider.
https://ia.acs.org.au/article/2025/popular-free-vpn-caught-spying-on-users.html
